Our assessment on recent reports by Pew Research are available to CTOvision Pro subscribers at:
- Net Threats: Nation-States and Security
Context for the CTO, CIO, CISO and Data Scientist
Our assessment on recent reports by Pew Research are available to CTOvision Pro subscribers at:
Michael Riley and Jordan Robertson published an important piece for Bloomberg news titled:
UglyGorilla Hack of U.S. Utility Exposes Cyberwar Threat
This well researched piece provides context on the threat I believe all technologists should understand. In fact, it is so important, I think every citizen should read it and think about its implications.
A preview from the piece:
Somewhere in China, a man typed his user name, “ghost,” and password, “hijack,” and proceeded to rifle the computers of a utility in the Northeastern U.S.
He plucked schematics of its pipelines. He copied security-guard patrol memos. He sought access to systems that regulate the flow of natural gas. He cruised channels where keystrokes could cut off a city’s heat, or make a pipeline explode.
That didn’t appear to be his intention, and neither was economic espionage. While he was one of the Chinese officers the U.S. charged last month with infiltrating computers to steal corporate secrets, this raid was different. The hacker called UglyGorilla invaded the utility on what was probably a scouting mission, looking for information China could use to wage war.
UglyGorilla is one of many hackers the FBI has watched. Agents have recorded raids by other operatives in China and in Russia and Iran, all apparently looking for security weaknesses that could be employed to disrupt the delivery of water and electricity and impede other functions critical to the economy, according to former intelligence officials with knowledge of the investigation. The incursions spurred a debate in the Obama administration over whether and how to respond, and raised alarms among lawmakers briefed on the incidents.
Read more at: UglyGorilla Hack of U.S. Utility Exposes Cyberwar Threat
I’m reminded this is a perfect example of something Matt Devost has been talking about for years including at the first FedCyber Summit (http://www.fedcyber.com). For additional context, check out this blog post discussing attacks against critical infrastructure:
http://www.oodaloop.com/
That is totally spot-on, don’t you think?
We track these and many related issues in our CyberWar site.
For more on these topics see the CTOvision Guide to National Security Technology and
Why does security have to be so onerous? Is this password secure enough: Mxyzptlk? Wait, that might be vulnerable to a comic book dictionary attack (bonus points for Superman fans), so let’s add some numbers and special characters: M4xyZ!ptL#K. Not bad, but suppose policy requires 12 or more characters; we have to pad the password: 0M4xyZ!9ptL#K. Now that’s secure – good luck remembering it!
We’ve migrated to a userid-password society; as we’ve added layers of security, we password-protect each layer: PC (and now device), network, enclave, application, database, and storage (encryption). Don’t use the same password for everything, because if the bad guys crack one, they own you. We’re not done yet, though – badges for physical access, PKI, USB keys, SmartCards, soft certs, biometrics, Network Access Control, firewalls, IPS/IDS, SIEM … I could go on and on. As you try to simplify the user experience and reduce friction, the cost for security goes up. Userids and passwords are almost free. It’s much easier to use biometrics or a SmartCard to identify yourself to a system or application. However, those solutions require fingerprint readers, better encryption, key management programs, and card provisioning systems, which also translates to more people needed to manage the security infrastructure. A telling example is the Department of Defense and its approach to mobile security. After investing in deployment of secure physical and cyber access via the Common Access Card (CAC), it made sense to leverage that investment in the mobile realm. However, to use CAC with an Apple iPhone, you need to buy a sled – an iPhone case with integrated card reader. The solution works well, however the sled costs more than the iPhone!
Instituting secure computing behavior can be ingrained, but it has to be built into both policies and culture. Working in secure government spaces for over 30 years, I lock my computer screen at home whenever I step away, have a strong password on my WiFi network, encrypt sensitive personal data, and have mirrored hard drives in my Network Attached Storage (NAS) device. However, that behavior is somewhat “old school” and the product of a very focused environment. Today’s computing culture is characterized by instant-on, always on, and always connected. Anything that slows you down, like having to enter a PIN to unlock your phone, is friction.
Can we overcome the friction of security? There are some attempts to improve usability, with an accompanying decrease in the strength of secure solutions. Referring back to the CAC, and SmartCards in general, the National Institute of Standards and Technology (NIST) has published a draft of Special Publication (SP) 800-157, “Guidelines for Derived Personal Identity Verification (PIV) Credentials.”
Instead of dealing with the additional cost and usability issues of a sled, you can derive a credential from the original cert that resides on your CAC or PIV card. That derived credential is transferred to a mobile device’s internal storage or microSD card, and can be used to authenticate an individual to an organization’s resources. The derived credential isn’t as strong as the original because it’s cryptographically removed from the cert that was vetted and checked through a strict, formal process. However, the derived credential has less friction.
I’ll use another mobility example here, just because computing is becoming more and more portable as devices incorporate improved and additional capabilities. The primary method for protecting your device against tampering today is password or PIN. No one likes having to enter that PIN – it takes an extra 2-3 seconds of focused attention. Definitely not instant access! Plus it’s another password to remember (if you happen to have separate passwords to access accounts of different sensitivity)! So Apple came up with Touch ID on their iPhone 5s. Once you register a fingerprint, it’s a simple touch to the main button to unlock your device. Less friction equals better user experience while providing a better level of security.
There are other innovative solutions coming to market that embrace the idea of frictionless security. The main concept is to leverage big data to determine the unique identity of an individual based on his or her behavior. Over time, our use of devices and network resources will form a pattern; no two people should have the same behavioral patterns. One company that’s developed this approach is ThreatMetrix.
Their two-factor authentication solution consists of a unique device ID and the big data pattern associated with it. The solution is intriguing – if my behavior can be proven to uniquely identify me (what ThreatMetrix calls a Persona ID), then my access and interaction with network resources could be frictionless.
Relating back to my previous blogs on continuous monitoring and the IoT, this frictionless security will become even more important in the near future. Today, you log into work accounts (network, financial, remote access, personnel, maybe more) and home accounts (WiFi, shopping, travel, financial, social networks, definitely more) with at least userid/password, and possibly something more secure (two-factor, multi-factor). Imagine having to do the same for your refrigerator, thermostat, home security system, and automobile. As more computing devices and sensors become integrated in our daily lives, security becomes even more critical in protecting our privacy and safety. We have to develop security methods that are easy to use, yet provide sufficient protections to keep us safe. The equation needs to be Modern Security = Frictionless.
This post first appeared on George Romas’ HP Blog
Today, the United States Department of Justice indicted five Chinese military officers related to alleged cyber espionage against U.S. companies. At the same time, John T. Chambers, Chairman and CEO of Cisco Systems, sent a letter to President Obama arguing that NSA efforts to undermine global Internet security undermine the future of the Internet and the United States’ technology industry. The two developments point to a number of possible implications for the U.S. government’s ability to protect companies from foreign espionage, as well as the future of the ongoing U.S.-China cyber dispute.
First, disclosures over the last year that indicate that NSA engages in cyber espionage against foreign companies help to bolster claims that the U.S. lacks credibility when confronting China about its engagement in economic espionage. This, in turn, undermines the United States’ ability to protect its companies from other states’ military and intelligence agencies.
We know that NSA has targeted companies in a number of countries, including China. Though no evidence has been presented that the U.S. government passes this information directly to U.S. companies–the primary basis of its complaint against China–it is nonetheless clear that its own economic espionage can benefit U.S. companies indirectly.
For example, NSA has targeted the servers of Chinese telecommunications equipment manufacturer, Huawei, while U.S. officials have warned against the use of that company’s products for fear of the kinds of “backdoors” we now know that NSA sometimes plants in Cisco equipment. Ultimately, the Chinese company decided to pull out of the U.S. market, citing the difficulties caused by such warnings. Even if the U.S. government did not pass Huawei corporate secrets directly to its U.S. competitors, driving them from the marketplace certainly provided an indirect benefit nonetheless.
Next, we also know that NSA surveillance has aided the U.S. in trade negotiations. The United States having a better chance of getting its way in such negotiations is certainly a benefit to U.S. industry, even if intelligence gathered from foreign companies and officials is never passed directly to U.S. companies.
But these benefits must be weighed against the potential harm done if or when others learn of such activities. In this case, we see the possibility that the benefits of NSA targeting foreign companies could be outweighed by a diminished capacity for the U.S. to protect its own companies when subjected to the same kind of behavior–or worse, which is what is alleged against China–by foreign intelligence agencies.
Predictably, China is taking advantage of our newfound knowledge of NSA targeting of its companies in its official response to the U.S. indictment, alleging that China is the true victim, not the United States.
None of this is to dismiss the possibility or seriousness of the actions for which the Chinese officers have been indicted. But to the degree that NSA actions lend credibility to the Chinese counter narrative, they represent one more way in which NSA surveillance has harmed U.S. companies.
But there are implications beyond the ability of the U.S. to protect its companies from foreign espionage and theft of intellectual property. As Attorney General Eric Holder noted, this is the first time the United States has taken this kind of action. As such, it sets a new precedent with serious potential consequences.
First, this is an escalation of U.S. efforts to deal with cyber threats using the criminal justice system. We can see this also in the FBI’s arrest of almost 100 hackers around the world today. Thus far, as I have noted many times, U.S. cybersecurity rhetoric, especially as it relates to China, has been dominated by talk of “cyber war.” This is in contrast to the reality that most cyber incidents are more properly characterized as instances of crime or espionage. So, perhaps this move signals a shift away from such bellicose cyber rhetoric.
Second, though a move away from war rhetoric should be welcomed, an aggressive pursuit of foreign military and intelligence officers for cyber crime in the wake of the NSA revelations could open U.S. officials to similar indictments from governments whose companies have been targeted by NSA. Will we see China or Brazil “naming and shaming” NSA employees? Only time will tell.
Third, if the Chinese are as persistent in carrying out espionage against U.S. companies as government officials insist, it is hard to imagine that this indictment will curtail those activities to any significant degree. Instead, what we have seen thus far is China suspending its participation in the Sino-U.S. network working group, which was meant as a forum for the two countries to work on resolving differences in the area of cybersecurity. This is a possibility that U.S. officials must certainly have anticipated. If so, the decision to proceed with the indictments could indicate that the working group was not succeeding in its mission and that the U.S. felt the time was right for an escalation in the ongoing cyber dispute.
Whatever the case, today’s events should serve to highlight the difficulties in using the power of the national security state to promote and protect the interests of U.S. industry. These actions can turn out to be a double-edged sword or to work at cross purposes to one another. Finally, today’s events also mark an important turning point in the ongoing cyber dispute between the United States and China.
Threats to our information are not only from malware or brute force hacks or social engineering. Criminals are motivated to look for every advantage. Sometimes we read about very sophisticated attacks against hardware that require advanced engineering. But attacks don’t really have to be sophisticated to be successful. Two relatively easy to execute attacks were recently highlighted by the New York City Metropolitan Transportation Authority.
Their press release is provided below. But first check out these incredible photos:





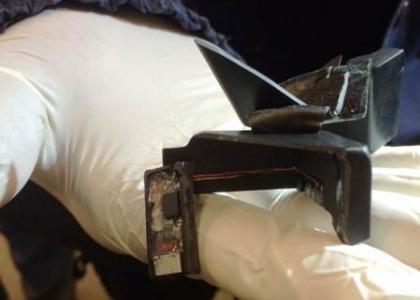

More from the MTA (10 April 2014):
MTA New York City Transit Reminds Customers to Watch for Scammers Who Target MetroCard Vending Machines
 platform at Columbus Circle.
platform at Columbus Circle.
Other Resources:
Spy Sites of New York: A Guide to the Region’s Secret History
Foreign Spies Make Recession Worse and Steal Part of Our Future
Who Is Spying On Me? A taxonomy of spies in the modern technology landscape
Advancing Genomics Through Big Data Studies: An Interview with Dr. Mark Guyer of NIH
We have previously discussed research and analysis we did for the Cyber Conflict Studies Association on the many “Wake-Up Calls” the nation’s policy makers have declared themselves to have had regarding cyber security. If history is any predictor of the past, we will still be getting these wake-up calls long into the future.
We want to change the future, of course. Doing that will require that we address the problems with Cyber Threat Amnesia our institutions suffer from.
As an aid to changing the future, please review this list of cyber security “wake-up calls” and consider ways we can collectively learn to stop repeating the same mistakes. I would love to get your feedback on this list.
This is not all major events, just those widely reported to be “wake up calls” for the nation.
Of course the reason to publish this list is not to make fun of people for using the term “wake up call.” The reason to publish the list is to get your brain deeper into the game. Maybe there is something you can do to prevent Cyber Threat Amnesia. Maybe you can suggest action to current community or government or business leaders? Or maybe you can find ways to educate policy makers or Congress or the American public? Or maybe you have other ideas for stopping this madness of forgetting about the threat.
 In the lead-up to possible airstrikes against Syria, a contradiction has emerged in the U.S. public policy debate about the prospective uses and impacts of cyber weapons. The use of such weapons against the United States is portrayed as potentially catastrophic and as an act of war. Used against a potential adversary, the same weapons are portrayed as a bloodless alternative to traditional airstrikes. But years of cyber-doom scare stories undermine the case for cyber weapons as a humanitarian alternative to traditional airstrikes.
In the lead-up to possible airstrikes against Syria, a contradiction has emerged in the U.S. public policy debate about the prospective uses and impacts of cyber weapons. The use of such weapons against the United States is portrayed as potentially catastrophic and as an act of war. Used against a potential adversary, the same weapons are portrayed as a bloodless alternative to traditional airstrikes. But years of cyber-doom scare stories undermine the case for cyber weapons as a humanitarian alternative to traditional airstrikes.
For years, policy makers and cyber security experts have warned of a growing cyber threat to the United States from any number of foreign actors. Such warnings are often accompanied by cyber-doom scenarios describing the potential impacts of cyber attacks in frightening terms. In these scenarios, cyber attacks on critical military and civilian infrastructures are predicted to have catastrophic results on par with natural disasters or the use of weapons of mass destruction. Images of 9/11, Hurricane Katrina, the Indian Ocean Tsunami, Super Storm Sandy, Pearl Harbor, and nuclear detonations are used to raise the alarm and motivate a response.
With the potential effects of cyber attacks framed in this way, it is unsurprising that the United States has said it would consider such attacks an act of war justifying the use of military force in response. Indeed, U.S. policy even seems to indicate that nuclear weapons remain on the table as a possible response to a particularly damaging cyber attack.
Recently, however, some commentators have argued that cyber attacks could provide a bloodless, non-military alternative to the airstrikes being considered in response to the Assad regime’s use of chemical weapons. Cyber attacks, they argue, can and should be used to take down Syrian civilian and military critical infrastructures, such as the electrical grid, military command and control, and air defense systems.
Others have gone so far as to argue that the use of offensive cyber attacks against Syria could help to repair the United States’ image in the wake of almost daily revelations about its efforts to surveil and militarize cyberspace. Jason Healey of the Atlantic Council, for example, has argued, “The world is increasingly seeing U.S. cyber power as a force for evil in the world. A cyber operation against Syria might help to reverse this view.”
This possibility seems doubtful at best. Secretary of State John Kerry has already been criticized–and rightly so–for his assertion that asking for permission to bomb Syria “is not asking you [Congress] to go to war.” By any definition of war, from Clausewitz to international law, what Kerry and the President propose is war. What’s more, we can be certain that if another nation struck the United States with the kind of strikes being proposed for Syria, U.S. political leaders would not hesitate to call them an act of war. They would be right to do so.
Similarly, a cyber attack launched by U.S. military personnel of precisely the kind that the United States has said it would consider an act of war is unlikely to be seen as a humanitarian, non-military alternative to war. Instead, it will be seen as a contradiction at best, hypocrisy at worst.
This is not to say that cyber attacks would not be less damaging than a traditional airstrike. They most likely would be. Indeed, I have argued that the cyber-doom scenarios so prominent in U.S. cyber security discourse are unrealistic representations of what can reasonably be achieved with cyber attacks.
But I have also argued that this overheated rhetoric is potentially dangerous in and of itself. It narrows the scope of our thinking about the cyber security challenges we face, limits the range of possible responses, and instills unrealistic expectations of what can be achieved via the use of cyber attack.
The United States’ overheated cyber rhetoric might yet come back to haunt it. After years of framing cyber attack in terms of war and large-scale natural disaster, policy makers might find it difficult to authorize such an attack and then be disappointed when the results do not live up to the hype. A summer of revelations about NSA surveillance and militarization of the Internet have angered many around the world. In this context, the use of the very cyber attack techniques that the United States has described as acts of war, and in a military strike that is wildly unpopular among Americans and Europeans, is likely to do more harm than good when it comes to repairing the image of U.S. cyber power at home and abroad.
(This post also appears at Forbes.com.)
A team of researchers at the University of Texas at Austin recently conducted an experiment on counterfeit GPS signals. During this experiment researchers used a custom built GPS spoofing device to send fake signals to a yacht, which in turn sent this giant 213-foot boat off course. And the worst part about this is that these counterfeit signals did not trigger any alarms!
When out at sea, a crew’s sense of the ship’s location is based completely off of GPS signals, and these signals are broadcasted from orbiting satellites. So during this experiment, a researcher was able to command a spoofing device to transmit faint fraudulent signals to the ship’s antennas. The researcher then increased the strength of the signals until they were stronger than the other satellite signals, thus gaining control of the ship’s navigation system. Because the takeover was stealthy and done slowly, no alarms were triggered. Once in control of the navigation, the researcher entered a 3-degree course change, which then caused the ship’s navigation system to report a slight drift. In reaction to the reported drift, the crew manually applied a course correction. Instead of correcting the course, the crew was actually steering off course, and onto the researcher’s intended fake route.
There are two main worries now, first is the fact that the GPS alarms were not triggered, and second is that this vulnerability might not be limited to just yachts. Users of any semi-autonomous vehicles, like airplanes, have come to trust their autopilot systems, and these systems could be at risk of being hacked from afar. There are some ways to prevent such attacks, like encrypting GPS signals. The US military encrypts their GPS codes differently than civilian GPS codes, resulting in less hackable GPS systems. Other options are to adjust algorithms that identify spoofing attempts or to strengthen GPS signals so that other signals won’t be able to overpower them.
Having a better understanding of how these GPS systems work is an easy way for everyday users to prevent these potential hacks. Solutions are in the mix, so the time for panic is NOT now. Though if you were planning on throwing out that old worn out paper map that you keep in the glove compartment, maybe now isn’t the opportune moment. Keep it around just incase, you never know when you will be without GPS connection.
To read more about the GPS Spoof, click here.
And see the video here:

This post is part of our Intelligent Enterprise series, which providing insights aimed at corporate strategists seeking competitive advantage through better and more accurate decision-making. The first post provided foundational insights into A Practitioner’s View of Corporate Intelligence. This one dives into actionable recommendation on ways to optimize a corporate intelligence effort. It is based on a career serving large scale analytical efforts in the US Intelligence Community and in applying principles of intelligence in corporate America.

Like so many others in the national security domain I am tracking what I can about the new US Space Force, the newest US military force. I believe their mission is important and establishing Space Force was the right move. Space is, by definition, a domain that will require deep technological expertise to enable mission […]

Editor’s note: We are aiming this tutorial at the non-technical person. Please share with anyone in your life who could benefit from this. -bg Cyberspace is a complex domain and our adversaries are always seeking new ways to steal information or spread their malicious code or hold our data for ransom. This is the big reason […]

Technology is advancing pretty fast, at times influenced by the exciting world of Science Fiction. This video captures 10 of the tech developments first seen in SciFi that are available now. A key point of this, if you want to know what is in our future, watch more SciFi!

Tom Loftus provided an insightful review of some of Super Bowl ads in the 4 Feb 2019 Wall Street Journal. Like AI parody in SNL, these ads really poked fun at computers: Seriously, did anyone catch the commercials? If the Super Bowl is the zeitgeist, then it is safe to say that America is not […]

HBO’s Westworld is a modern take on the Michael Crichton SciFi tale of a robotic amusement park. The HBO version has a new twist. The creators/writers were all exposed to years of Twitter, which has influenced every episode and the entire arch of two seasons of the show. Now that season two is wrapping up, […]