Social engineering is one of the most problematic attack techniques to combat. It preys on our nature as human beings and is therefore difficult to counter by using technology. User education is most effective at stopping a social engineer. Users who are aware of the potential for social engineering attacks and learn to recognize them can use simple methods to thwart these attacks successfully. Phishing is a type of social engineering that’s executed through unsolicited email messages.
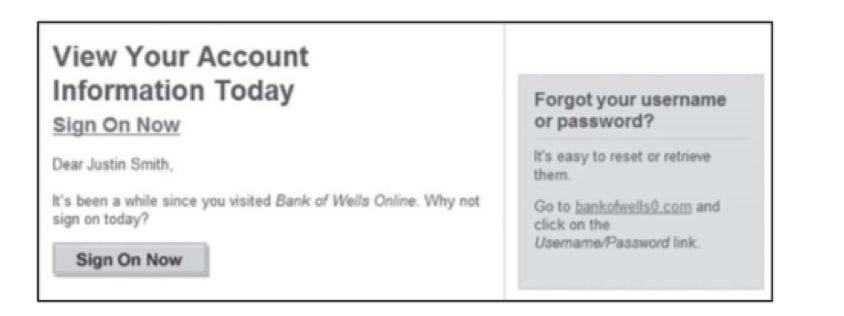
Notice that the email message looks as if it came from the user’s bank. The formatting most likely matches that of the bank’s typical email messages. The name of the bank looks correct, and the user’s name even looks properly addressed in the message.
At first glance, this email message looks legitimate. It appears as though the bank sent it to ask the customer to log in to his account. However, notice that the link provided on the right side of the message has an extra 0 in it. If you hovered your mouse pointer over the Sign On Now button, you would discover the same thing. The email message did not originate from the bank. It’s actually intended to direct the user to a malicious website. The look and feel of the rogue website would be similar to the look and feel of the actual banking site, but a criminal, not the bank, would receive any data the unwitting user entered. With the user’s name and password, an attacker could go to the real banking site, access the victim’s account, and steal money. If the victim uses the same user name and password on many sites, the cybercriminal has also obtained credentials to many of that person’s accounts. The results could be catastrophic for the victim. Damage could range from petty monetary theft, to a complete drain of financial resources, to full-blown identity theft.
Should I or Shouldn’t I?
Users must be educated to understand that it’s typically not safe to divulge sensitive information. For example, they should never respond to unsolicited requests for sensitive information. The request ploy may vary, but the response should remain consistent. Don’t do it!
If a user initiates contact, a request for sensitive information is usually warranted. For instance, if you call your bank to request a change to your account, the bank first verifies your identity. The bank may do this by asking for the passcode you selected when you established the account. In addition, the bank would ask for other information to authenticate you as a valid account holder, such as your name, account number, and possibly address or phone number.
The same concept holds true for websites that are password protected. Let’s say you type the address of your bank or email provider in a web browser and press Enter. You can typically be assured that you’re connecting to the authentic site. However, if your PC is infected with malware that redirects your web requests, you may still be at risk. This is one reason that an up-to-date anti-malware program is also a must-have for safe computing.
Look for SSL to Keep You Safe
It’s relatively easy to ensure that you’re in a secure computing environment. Before entering any sensitive information into a web form, look for an indication of Secure Sockets Layer (SSL). SSL is an encryption technology that, among other things, lets you connect to websites securely. (You’ll learn more about encryption later in this chapter.)
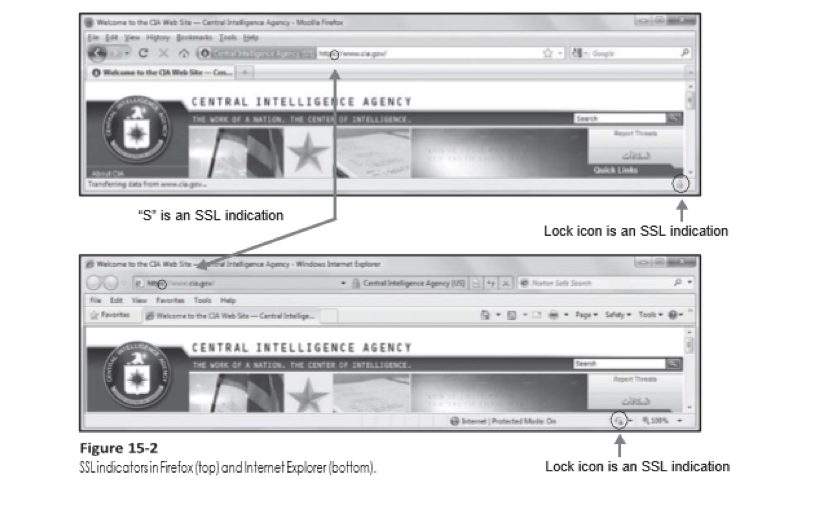
Different web browsers display different SSL indicators. Figure 15-2 shows the SSL indicators in Mozilla Firefox and Microsoft Internet Explorer. Typically, a lock icon is displayed somewhere in the browser screen and the website address is prefaced with the letters https. The letter s in https indicates that SSL encryption is in use.
If a connection is not secured with SSL, it transmits data across the Internet as clear text. Clear text is unencrypted text that can be read by anyone who captures the transmission.
If you have followed best practices and taken safety precautions, you may decide to follow through with an online activity anyway. However, think carefully about what kind of site you’re visiting and what kind of information you’re being asked to provide. In some circumstances, you should be skeptical and suspicious. If you doubt the legitimacy of any situation, refuse to provide sensitive data to the requesting party. Chances are a cybercriminal is trying to trick you into providing private information.









