Wireless security is all about implementation. The vendors implementation of the stack, the implementation of the security protocol standards in your OS that you have deployed to your users, the ways that the radios work, and the settings you’ve chosen for your network. Unfortunately, wireless security is generally weak (unless we’re talking about a properly-deployed WPA2-PEAP setup, which we’ll go over in another post) because of the way network associations are performed in the protocol standard, the way networks are discovered, and the fact that management frames are not encrypted.
Your Previous Connection History Leaked:
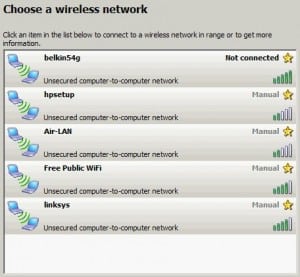
When you first decide to turn on your wifi, you start leaking information about yourself. How much and what you leak depends on your wireless driver, operating system, and the networks that you’ve connected to in the past. In general, you leak two pieces of information: your uniquely assigned network card number (MAC Address) and the names of networks you’ve previously connected to.
Why do you leak the names of networks you’ve connected to? It’s supposed to be a feature — the operating system is attempting to see if you’re around any of those networks by sending out a beacon request to see who responds to them. If someone, anyone responds to a beacon, well, that must be a network you know! Connect! It works this way by design to allow you to roam between multiple access points for the same network.
Attack 1 – Karma:
There’s a problem with this leakage — what happens when someone starts responding to any/every network beacon request? That’s when you start seeing your home network name at Starbucks, ten miles away! This attack is sometimes known as Karma.
If you’re thinking “The network i’m connected to uses encryption so I’m safe”, you’re wrong. Potentially any of your past network connections that weren’t encrypted are targets if they are beaconed for by your hardware. That’s why I delete wireless network connections that are unencrypted when I am done using them (if I use them at all).
It seems that Apple hardware is most susceptible to attacks of this nature. They are chatty by nature and almost always query the wireless around you looking for previous connections. Of Apple products, iPhones are consistently the worst and are well-known in the wireless security community for their promiscuousness. Older versions of XP, Android, and many embedded devices are also good targets for this kind of attack. Generally, up-to-date Windows and Linux aren’t as vulnerable to this, but everyone is vulnerable to another kind of attack against unsecured wireless connections — the Evil Twin.
Attack 2 – The Evil Twin:
The evil twin attack requires a two strong radio signal cards and a wireless network with the same name as a nearby but preferably weaker-signal wireless network that you want to attack.
You utilize one radio card to find clients of the target wireless network and remove them by abusing the WiFi connection protocol. Specifically, your wireless card talks on the same radio frequency channel impersonating the access point of the target network and tells its clients that they are disconnected.
Confused, the disconnected clients start looking for the wireless network again, but this time, your radio responds to the request louder and more quickly than the other network — forcing victims to connect to you. If you provide internet to these clients and the exchange is quick enough they may never even notice that they have been connected to your malicious access point.
The disconnection attack works even if your targets are connected to an encrypted wireless network, and may cause them to leap from that encrypted network onto an unprotected network that they’ve previously connected to and are now looking for since they’ve been disconnected. This happens because the management frames (the parts of the wifi protocol that allow you to connect and disconnect from a network) are not encrypted in (most) wireless encryption standards.
How do I test my vulnerability to this?
I’ve developed a software package to make testing wireless vulnerability to these well-known attacks very easy for someone acquainted with Linux. If you understand how to get your network interfaces working under linux, you should be able to use this software package.
WAT : Wireless Attack Toolkit
The Wireless Attack Toolkit automates the Karma and Evil Twin attacks and throws in a few other attacks for good measure. Normally you’d have to set up IPTables, compile the hostapd-karma software, configure a DHCP server, and a dozen other small things, but these aspects are all taken care of for you — you just specify which interfaces will be performing which tasks (connecting you to the internet, acting as the fake access point, attacking the victims) and you’re off to the races. You can watch people come in via the DHCP server, watch where they’re browsing via the DNS server, and attack their web browsers via some built-in software.
One feature of this toolkit is that this software can run on a Raspberry Pi for ~$260 in equipment costs. With a battery pack providing power and a mobile phone providing internet, the attack package can hack people onto your wireless connection and place them under your control for over 8 hours on a single charge. That’s a lot of iPhones.
Download the Wireless Attack Toolkit here: https://sourceforge.net/projects/piwat/
Check out my Defcon Presentation about WAT
Note: To be most effective with the Wireless Attack Toolkit, you should change the static Malicious Access Point Name. I’m working on making that easier.
Legal Note: It may be of questionable legality to run this software in public locations.









